Redmond, Wa.—In a shocking turn of events, Microsoft CEO Bill Gates attempted to push the new Windows 11 update on loyal customers, only to have his plans backfire spectacularly. The update software, which was supposed to be a revolutionary step forward for the company, was instead met with widespread criticism for its condescending and insulting tone toward existing customers.

Despite Gates’ assurances that Windows 11 was a “game changer” and “the future of computing,” users were quick to point out that the update prompt was filled with arrogant and patronizing language. One user said, “I’ve been using Windows for over 20 years, and I’ve never felt so disrespected by a software update.”
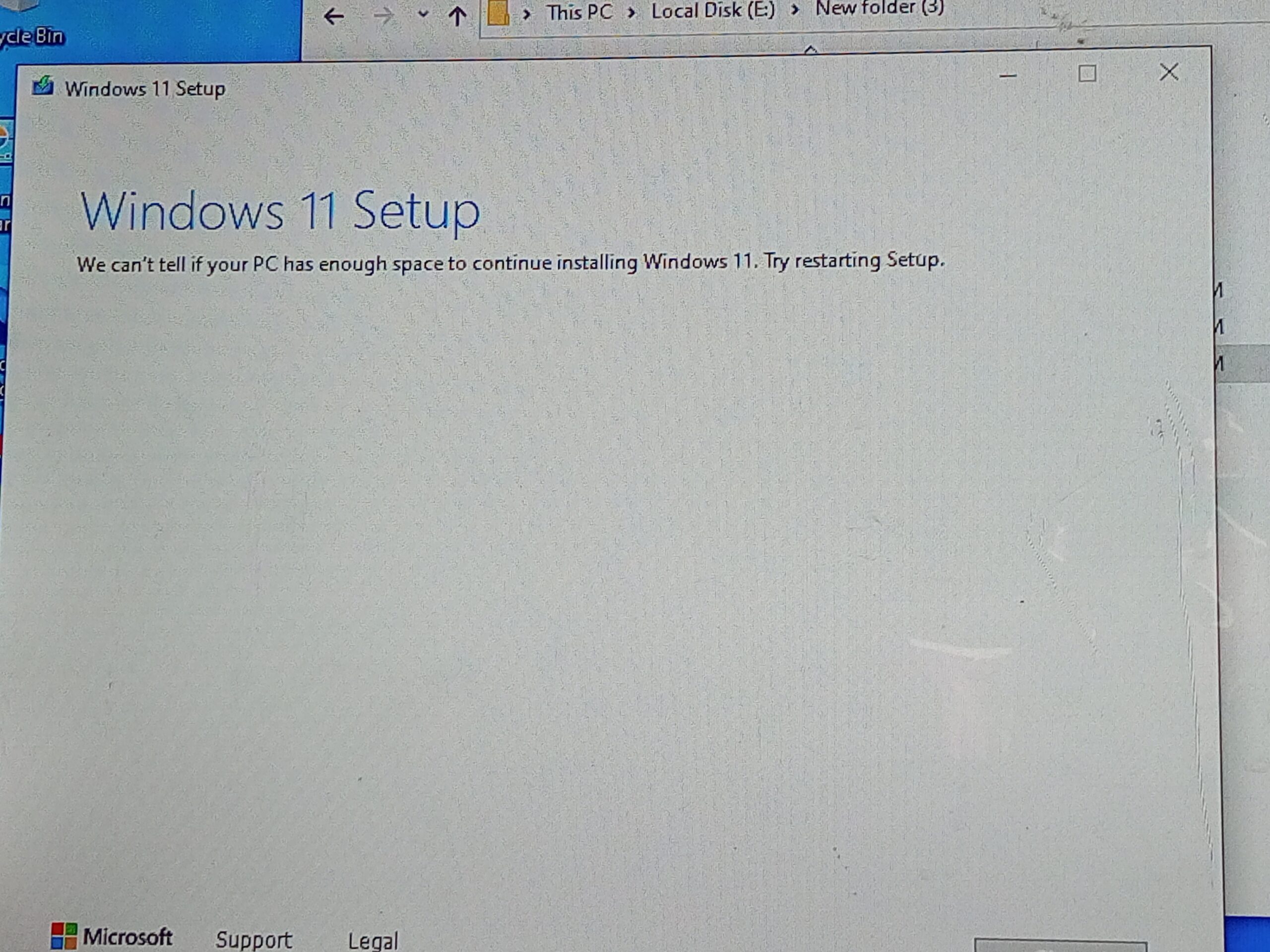
Adding to the frustration, many users reported that the update itself was riddled with bugs and glitches, making it nearly impossible to use. One user said, “Another layer of polish on the same old turd. I tried to install the update, but it just kept crashing my computer. I ended up having to roll back to Windows 10.”
In a desperate attempt to salvage the situation, Gates issued a public apology, saying, “I realize now that we may have come across as arrogant and out of touch. We want to assure our customers that we value their feedback and will do everything in our power to make sure that future updates are more respectful and user-friendly.”
However, it seems that the damage has already been done, as many users have pledged to never update to Windows 11, no matter how good it may be.
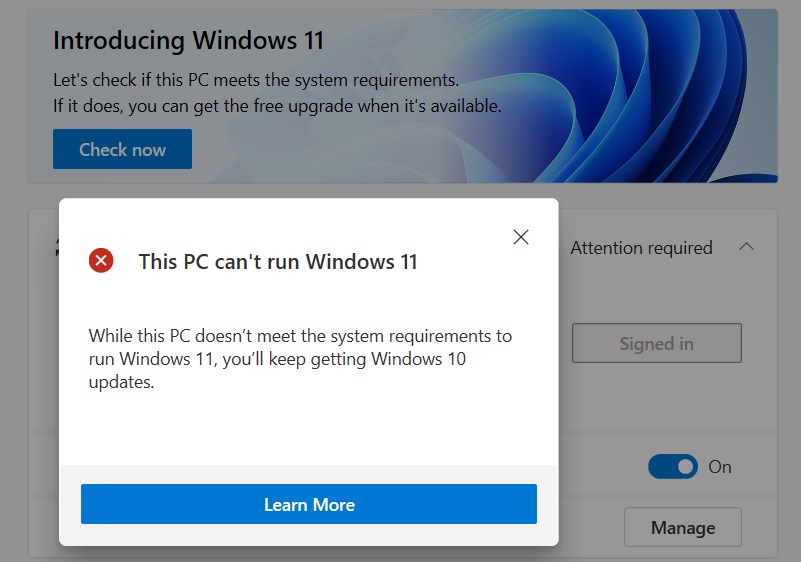
One imageboard user took to 4chan, saying, “I don’t care if Windows 11 is the best thing since sliced bread – which it isn’t – each iteration sets you one more click back from making your PC do what you want – I’ll never trust Microsoft again after this condescending update. My PC can’t run Windows 11? Great, I guess that means you’ll be leaving me alone, then.”
The incident serves as a cautionary tale for tech companies everywhere, reminding them that even the most cutting-edge technology can be undone by a single arrogant and out-of-touch update prompt.