TANGO DOWN!
Everything the Jester was once known for has been taken away. He has been castrated by Apache developers, posted an embarrassing music video which encompasses his feelings toward small children, and is now shitting himself in fear of Lebal Drocer, Incorporated.
 Recently, I met th3j35t3r in Barrett Brown’s empty tinychat room, where he bragged about taking the Chronicle down for a few days. Which is true, he did: by running a simple script against BlueHost, who we paid to host the Chronicle, he caused one of their servers to seize up and a whole bunch of their clientele’s websites went down with chronicle.su. And when I met him, he had just “quit hacking” – supposedly on a whim, so before I left him in there, I was sure to point out the true reason the attacks stopped:
Recently, I met th3j35t3r in Barrett Brown’s empty tinychat room, where he bragged about taking the Chronicle down for a few days. Which is true, he did: by running a simple script against BlueHost, who we paid to host the Chronicle, he caused one of their servers to seize up and a whole bunch of their clientele’s websites went down with chronicle.su. And when I met him, he had just “quit hacking” – supposedly on a whim, so before I left him in there, I was sure to point out the true reason the attacks stopped:
The script Jester used to attack us – and many others – is now obsolete since Apache developers updated their software. No big deal, just a little update and web hosts everywhere are fine again. We updated and now we are fine. But the Jester’s afraid BlueHost and Lebal Drocer are pissed off about it. And he’s probably right. Sure, maybe we provoked him, but this is what happens when you attack the 1%. They do not forgive. They do not forget. So just because he took us down in August doesn’t mean our old host doesn’t want their fucking money now.
Take one quick moment to absorb our small victory, for we have beaten the Jester at his own silly game. You see, the Jester is a terrorist. His goal is to create terror. For example, he wants to chill our speech – by attacking our site, he hoped to make us afraid to write. Obviously, that didn’t happen. But now he’s afraid that our team of lawyers are coming after him in the name of Lebal Drocer, Inc. [Editor’s note: Fact is, he attacked us on shared hosting, on one of the largest webhosts in the world. Did “the jester” really think Bluehost would tolerate him downing thousands of clients’ sites at once?]
What a cowardly bitch. He took everything down, including his picture of the cease-and-desist order they sent him. That means Bluehost actually knows the identity of “the jester.” But we don’t, and neither do you. Still, we can characterize him for you anyway, using all the information we do have.
Who is th3j35t3r?
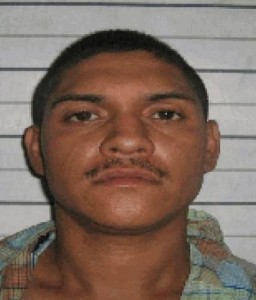
The Jester, a known pedophile, is an otherwise sexless man – a “script kiddie” that somehow figured out he could bloat up outdated Apache servers to uselessness. This is achieved by holding a large number of connections open with the server at one time. He is a longtime fan of the Insane Clown Posse, who eroded his creativity before it ever had a chance to bloom. Having no web design skills, his only alternative was to destroy. So he went to “work.” But who to attack?
Over time, the fatass Jesterfag became so well known for torturing Urdu (language) Islamic website owners, he became widely recognized as the world’s most likely hacker to vote a third time for Bush and Cheney.
Later on, as he gained Twitter followers, he took on feelings of Unwarranted Self-Importance and pretended to harbor political convictions after the mainstream media assassinated Wikileaks for being better at journalism than them.
He soon claimed attacks on Wikileaks, as well as the Westboro Baptist Church of Trolling Art.
But he fucked up when I provoked him to attack us. If you’ve been reading up till this point, you know how: he took my bait, ultimately unleashing a ravenous team of coked up Lebal Drocer lawyers who seek to hunt him down like a runaway slave – they are on so much cocaine they’re representing the web hosts of jihadists.
The Jester thought he could bitch and complain to our host that we were running profanity and “slandering” his fake name. [ Editor’s note: libel is written. Slander is spoken. ] But he doesn’t know about the law and how there are no laws which protect false identities from libel.
If the Jester read more, he might have learned the laws before making an ass out of himself. But books are for faggots. Still, he is willing to pull Steinbeck quotes from wikiquote. #pseudointellectual #pedophile
Steinbeck wrote about the Great Depression – a time when men were men, and you didn’t fuck with other people’s accounts unless they were fucking with your moonshine operation. But if you did, you learned the hard way not to. The Jester, too, will learn.
The Chronicle always wins.
___
Mach2600 is a slut. Her #pussy stinks..
Anonymously37 gets dragged into our shit for the lulz. He has no idea why.
Mockingbird = sockpuppet of the sockpuppet, or #sockingbird